It is always better to be proactive when it comes to protecting the security of your network as the working of the entire company depends on it. Checking the potential points of exposure will enable you to identify the security loopholes which can be done with network vulnerability scanner free or network vulnerability scanner download. You will be able to download a network vulnerability scanner open source. These vulnerability scanners open source are very easy to use and are very user-friendly.
OpenVAS
This free software is an open source vulnerability manager that can be used to scan the network. This is a framework of many services and different tools that will offer comprehensive scanning solutions. It is very reliable and can be maintained on a permanent basis. The core of this SSL architecture is the OpenVAS scanner.
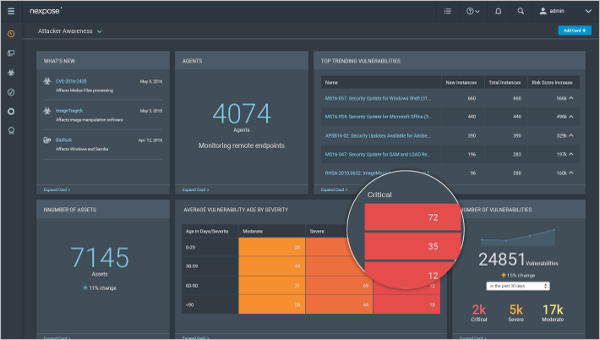
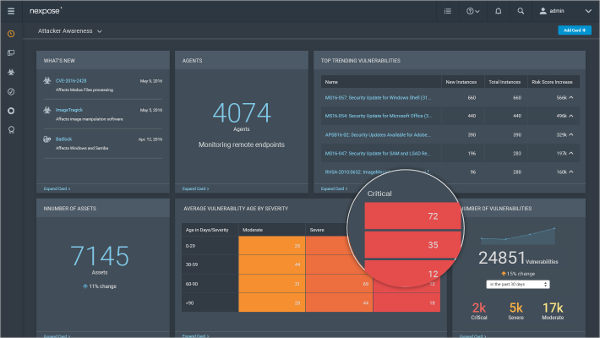
Nexpose
This premium software can be used to focus on the main risks that matter and also to reduce the total time that is required to manage a successful vulnerability program. It can be used to understand the weak points in the organization that would help in building a prioritized remediation plan to reduce the attack surface in the network.
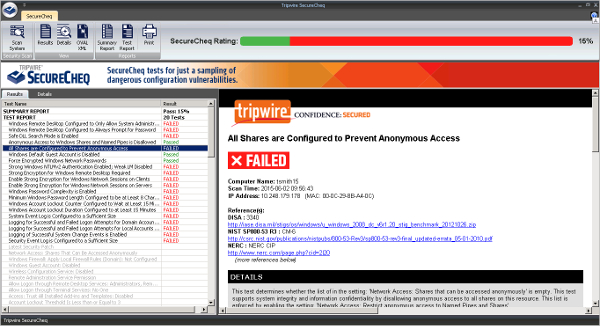
Tripwire SecureCheq
This premium software can be used to test the common configuration errors in the network and the various weaknesses in Microsoft Windows servers and desktops. It will help in managing the risks to ensure less downtime, reduce management overhead and also provide better performance. The overall cost incurred will also be reduced.
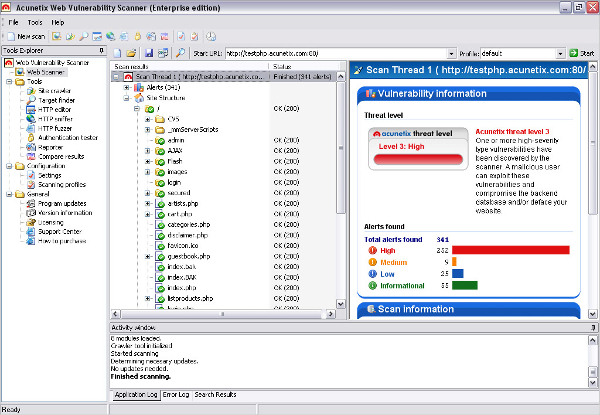
Free Network Vulnerability Scan
This free software can be used to rectify the network security vulnerabilities. It allows users to scan the servers for more than 35,000 vulnerabilities and audit the internet facing servers. It will ensure that the network is not running any illegitimate services and also identifies any vulnerable versions of those applications that are running on the server.
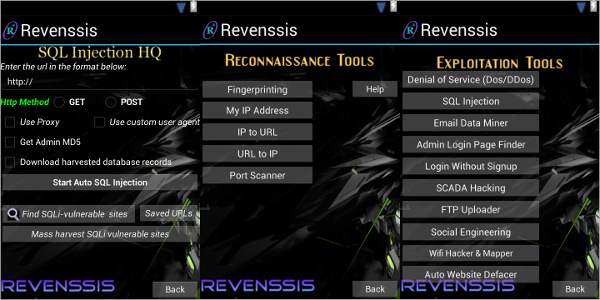
Revenssis Penetration Testing Suite for Android
This free Android app can be used for any computer and web application security purposes. It has a set of useful tools that will help in running web app scanners, vulnerability research labs, encode and decode tools, hosting tools, and forensic labs. Many types of Web Vulnerability Scanners are included and other scanners like XSS, DDOS, CSRF, SQL, etc. are also available. Remote and local files can also be scanned using this software.
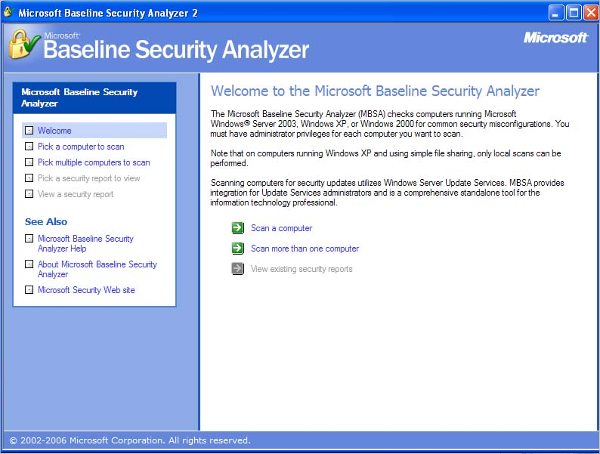
Microsoft Baseline Security Analyzer for Windows
This Windows software can be used for free to provide a streamlined procedure that will be able to identify the security updates that are missing and the common security misconfigurations. It will be able to run on Windows 8.1, 8 and also on Windows Server 2012 R2 and 2012.
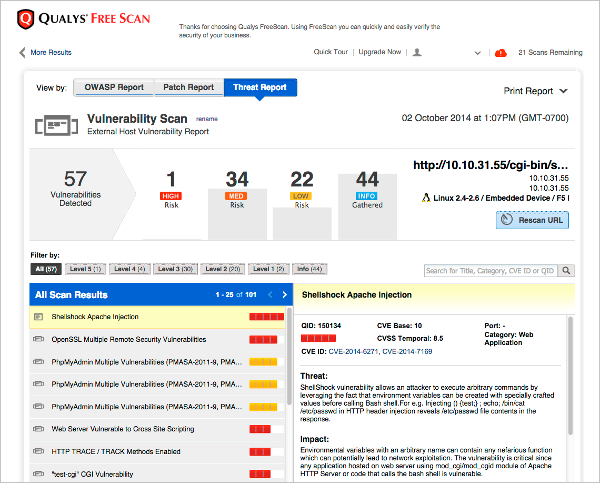
Most Popular Software – Qualys FreeScan
This free software can be used to scan the computers and apps that are on the network and Internet. It will be able to detect security vulnerabilities and patch the needed areas to fix them. Interactive scan reports can be viewed based on threat or the patches.
How to install Network Vulnerability Scanner?
Before installing, users have to make sure that all the system requirements are fulfilled and then the readme.html file can be viewed before running the file for the first time as it contains all the necessary system requirements, tool support options, and scan options. Then the file has to be downloaded and the installation can be started by running the program from the current location. It can also be saved onto the disk after which the installation file can be run.
This software will be able to ensure that all the services in the organization including mail and FTP do not suffer. It can be used to discover the information that the system is leaking by using some techniques like OS Fingerprinting, service probing and port banner grabbing. Additional information regarding the vulnerabilities and network problems could be obtained.
Related Posts
10+ Best Trust Accounting Software for Windows, Mac, Android 2022
10+ Best Patient Portal Software for Windows, Mac, Android 2022
13+ Best Virtual Reality (VR) Software for Windows, Mac, Android 2022
12+ Best Bed and Breakfast Software for Windows, Mac, Android 2022
15+ Best Resort Management Software for Windows, Mac, Android 2022
14+ Best Hotel Channel Management Software for Windows, Mac, Android 2022
12+ Best Social Media Monitoring Software for Windows, Mac, Android 2022
10+ Best Transport Management Software for Windows, Mac, Android 2022
10+ Best Other Marketing Software for Windows, Mac, Android 2022
10+ Best Top Sales Enablement Software for Windows, Mac, Android 2022
8+ Best Industry Business Intelligence Software for Windows, Mac, Android 2022
10+ Best Insurance Agency Software for Windows, Mac, Android 2022
10+ Best Leave Management Software for Windows, Mac, Android 2022
10+ Best Mobile Event Apps Software for Windows, Mac, Android 2022
10+ Best Online CRM Software for Windows, Mac, Android 2022